During Def Con 24 in LA ( hacking conference) researchers have shown a security gap exposed about 900 people of Android users to danger.
QuadRooter is a security gap recently discovered to affect any device that works with Qualcomm processors.
What is QuadRooter?
A 4 different points of vulnerabilities affecting Qualcomm processors. The driver which controls communication between chipset components.
Rooting:
Rooting means allowing smartphone users to have a special access to the system’s files. Phone owners attempt to do it for the aim of overcoming carrier and hardware limitations.
Many users deliberately root their devices in order to attain all these privileges. Experts say that it’s a high risk process and it allows hackers to easily access your device using the Qualcomm vulnerabilities using malicious apps.
Adam Donenfeld, a security researcher at Check Point, explained that these malicious apps don’t require any special access to exploit these vulnerabilities.
Phones that were affected by QuadRooter:

- Samsung Galaxy S7 and S7 Edge
- Google Nexus 5x, Nexus6 and Nexus 6P
- HTC especially HTC ONE, HTC M9 and HTC10
- LG Phones especially LG G4, LG G5 and LG V10
- Motorola Moto X
- One plus one, two and three.
How can it be fixed?
Unfortunately, it’s a major part of the software that comes pre-installed at the manufacturer and the only way for a fix is by an update from Qualcomm.
Users have informed Qualcomm with the issue and the company is in pursuit of solving all the exploits in all of the affected devices.
How to Stay Secure?
The first thing to do is that you should keep your device up to date.
Only use authenticated WiFi networks.
Read the app permissions to know more about what you’re installing.
Download apps only from Google play.
For more information:
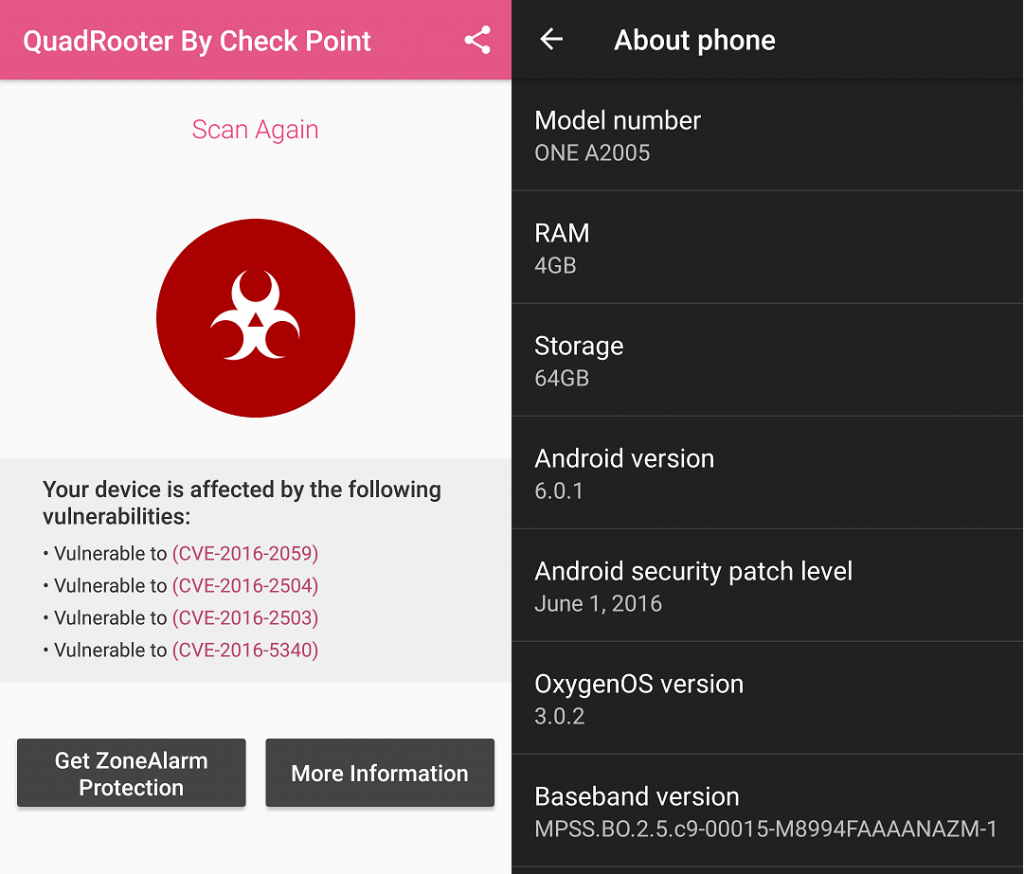
Users can find a free QuadRooter scanner app on Google Play which can tell you if these exploits are in your device.